Key Findings Lunar Spider has expanded its initial access methods by compromising vulnerable websites, particularly in Europe, using Cross-Origin Resource Sharing (CORS) vulnerabilities. These websites are then injected with a FakeCaptcha framework. The FakeCaptcha framework is introduced via a JavaScript script that generates an iframe, overlaying the original site's content with the attacker's FakeCaptcha page. … Continue reading Lunar Spider Expands their Web via FakeCaptcha
Category: Malware
OneNote Embedded URL Abuse
Whilst Microsoft is fixing the embedded files feature in OneNote I decided to abuse a whole other feature. Embedded URLs. Turns out this is something they may also have to fix.
OneNote Embedded file abuse
In recent weeks OneNote has gotten a lot of media attention as threat actors are abusing the embedded files feature in OneNote in their phishing campaigns. In this post we will analyze this new way of malware delivery and create a detection rule for it.
Analysis of a trojanized jQuery script: GootLoader unleashed
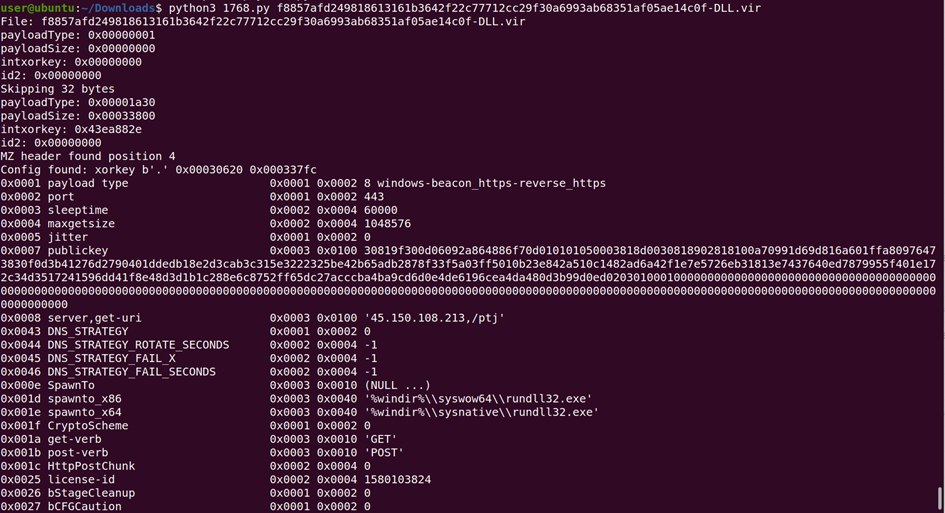
Update 24/10/202: We have noticed 2 changes since we published this report 3 months ago. The code has been adapted to use registry key “HKEY_CURRENT_USER\SOFTWARE\Microsoft\Personalization” instead of “HKEY_CURRENT_USER\SOFTWARE\Microsoft\Phone” (sample SHA256 ed2f654b5c5e8c05c27457876f3855e51d89c5f946c8aefecca7f110a6276a6e) When the payload is Cobalt Strike, the beacon configuration now contains hostnames for the C2, like r1dark[.]ssndob[.]cn[.]com and r2dark[.]ssndob[.]cn[.]com (all prior CS samples we … Continue reading Analysis of a trojanized jQuery script: GootLoader unleashed
Analyzing VSTO Office Files
VSTO Office files are Office document files linked to a Visual Studio Office File application. When opened, they launch a custom .NET application. There are various ways to achieve this, including methods to serve the VSTO files via an external web server. An article was recently published on the creation of these document files for … Continue reading Analyzing VSTO Office Files
Hunting Emotet campaigns with Kusto
Introduction Emotet doesn't need an introduction anymore - it is one of the more prolific cybercriminal gangs and has been around for many years. In January 2021, a disruption effort took place via Europol and other law enforcement authorities to take Emotet down for good. [1] Indeed, there was a significant decrease in Emotet malicious … Continue reading Hunting Emotet campaigns with Kusto